The VisitorsGate
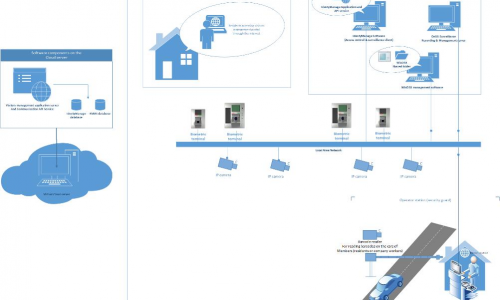
IdentyTech Visitors Management is an easy-to-use, web-based, enterprise class visitor management system. The IdentyTech visitor management system is also a part of IdentyTech access control solution which integrates a biometric access control terminals, video management, intruder alarm system management & much more.
How it works?
IdentyTech VisitorsGate™ system is a cloud based system. Each customer receives a proprietary domain address such as: comapanyname.visitorsgate.com. The hosts (such as residents or companies within the facility) will be able to access the system by this URL. It is not required to be on site in order to schedule a new visitors, hosts can access the system any time from anywhere via the internet.